Introduction: The Inevitable Cryptographic Shift
The quantum-safe transition to Post-Quantum Cryptography (PQC) is a present-day national security imperative. The advent of cryptographically relevant quantum computers (CRQCs) represents a fundamental paradigm shift, one that will render obsolete the foundational public-key cryptography protecting virtually all sensitive digital communications and stored data. This is not a distant, theoretical risk but an impending reality that demands immediate strategic planning and action from leaders across the public and defense sectors.
The primary catalyst for this urgency is the insidious threat of “Harvest Now, Decrypt Later” (HNDL). State-level adversaries are actively capturing and storing vast quantities of encrypted data today—including state secrets, defense plans, intelligence assets, and critical infrastructure communications—with the full expectation of decrypting this trove of information once a sufficiently powerful quantum computer is operational. For any data with a long-term secrecy requirement, the vulnerability is not a future problem; the compromise has, in effect, already begun.
In response to this existential threat, the global cryptographic community, spearheaded by the U.S. National Institute of Standards and Technology (NIST), has engaged in a multi-year, collaborative process to develop and standardize a new generation of quantum-resistant algorithms. The finalization of the first official PQC standards in 2024 marks the formal commencement of the global migration era, providing a stable, internationally vetted set of cryptographic tools that will form the new benchmark for digital security.
This report provides a strategic roadmap for public and defense sector executives to navigate this complex and mission-critical transition. It demonstrates how Kryptus’s BruitBlanc ecosystem offers a practical, certified, and sovereign pathway to not only achieve quantum-resistance but to build a lasting foundation of cryptographic agility, ensuring the long-term security and sovereignty of a nation’s most critical digital assets.
Section 1: The Quantum Threat to National Sovereignty
1.1. The End of the Public-Key Era: A Foundational Risk
For decades, the security of the digital world has been built upon public-key cryptographic systems like RSA and Elliptic-Curve Cryptography (ECC). These algorithms derive their strength from the mathematical difficulty of solving problems such as factoring large numbers or computing discrete logarithms on classical computers. However, the development of large-scale quantum computers will fundamentally break this security model. An algorithm developed in 1994, Shor’s algorithm, is specifically designed to solve these exact mathematical problems with exponential speed, making them trivial for a CRQC to overcome.
The impact of this cryptographic break is systemic and catastrophic. It compromises the core pillars of digital trust that underpin nearly every facet of modern government and defense operations:
– Secure Communications: The Transport Layer Security (TLS) protocol that protects virtually all internet traffic, from secure websites to API calls, relies on public-key cryptography.
– Virtual Private Networks (VPNs): The IPsec and other VPN protocols used to secure remote access and connect government facilities depend on these vulnerable algorithms.
– Digital Signatures: The mechanisms that verify the authenticity and integrity of software updates, authenticate user identities, and ensure the non-repudiation of official documents will be forgeable.
– Data Protection: Classified data, whether in transit across networks or at rest in databases, is often protected by encryption systems that use public-key cryptography for key exchange.
The failure of this foundational cryptographic layer would result in a complete breakdown of the digital trust and security infrastructure that modern nations depend upon to function effectively and securely.
1.2. HNDL: The Present Danger for Long-Term Secrets
While the threat of an active attack from a future quantum computer is significant, the most immediate and pressing danger is the HNDL attack vector. Unlike a conventional cyberattack that is often immediately detectable, HNDL is silent, passive, and happening now. Adversaries are exfiltrating and archiving encrypted data today, creating a latent threat that will only materialize years from now.
This alters the calculus of risk management. Traditional cybersecurity frameworks are often oriented toward responding to immediate, observable threats. HNDL decouples the security incident (the data theft) from its consequence (the data exploitation) by a significant time lag, potentially a decade or more. This creates a dangerous blind spot for risk models that may severely underestimate the long-term strategic damage being incurred today. For a defense organization, a weapon system blueprint stolen and stored now could lead to a critical battlefield vulnerability a decade in the future—a risk that is difficult to quantify but impossible to ignore.
This threat is particularly acute for the public and defense sectors, where information has an exceptionally long secrecy lifespan. National security strategies, diplomatic cables, military research and development, intelligence asset identities, and sensitive citizen data must often remain confidential for decades. Given that historical cryptographic transitions have taken upwards of 20 years to complete, waiting for a CRQC to become a reality before acting is no longer a viable strategy.
The recognition of this urgent threat is now codified in official government policy. Initiatives from the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the White House’s National Security Memorandum 10 (NSM-10), and guidance from the National Security Agency (NSA) all underscore the formal government mandate to begin the PQC transition immediately.
1.3. The NIST Standardization Process: Forging the New Defenses
The path forward is being paved by a rigorous, transparent, and global standardization effort led by NIST. Beginning in 2015, NIST initiated a public competition to select and standardize the next generation of public-key cryptographic algorithms resistant to attacks from both classical and quantum computers. This multi-year process evaluated 82 candidate algorithms from 25 countries, subjecting them to intense public scrutiny from the world’s leading cryptographers.
The selected algorithms are based on different families of mathematical problems, such as those involving structured lattices and cryptographic hashes, which are believed to be computationally hard for both classical and quantum computers to solve. The first finalized standards include:
– CRYSTALS-Kyber (standardized as ML-KEM): For key-establishment mechanisms, used to securely agree on a shared secret key over an insecure channel
– CRYSTALS-Dilithium (standardized as ML-DSA): For digital signatures, used to verify the authenticity and integrity of data and identities.
This standardization process is a crucial geopolitical endeavor. It establishes a common, non-proprietary, and freely available foundation for global digital security. Without such a standard, the world could face a fractured cryptographic landscape of competing, proprietary, and non-interoperable “quantum-safe” solutions. This would severely hinder everything from international commerce to coalition defense operations, which rely on a shared, trusted layer of secure communication. The NIST standards ensure that the future of digital security is built on a foundation of interoperability, a critical strategic goal for any entity operating in a global context.
Section 2: The BruitBlanc Ecosystem: A Certified Foundation for Quantum Resilience
2.1. The Strategic Imperative of a Trusted, Sovereign Core
A successful and defensible PQC migration cannot be built on unverified claims or proprietary, black-box technologies. For public and defense sector organizations, the cryptographic core of their infrastructure must be anchored in verifiable, internationally recognized certifications and standards. This is a non-negotiable requirement for establishing trust, ensuring compliance, and mitigating risk.
The Kryptus BruitBlanc ecosystem is an integrated suite of hardware and software cryptographic solutions designed to provide this trusted foundation. Crucially for government and defense clients, it is engineered as a sovereign solution, explicitly designed to be “free from surveillance laws” imposed by foreign governments, ensuring that a nation’s most sensitive data remains under its own control. The ecosystem’s components—the kNET Hardware Security Module (HSM), the CommGuard network encryptor, and the KeyGuardian portable cryptocomputer—work in concert to provide end-to-end, quantum-resistant protection for data at-rest, in-transit, and at the endpoint.
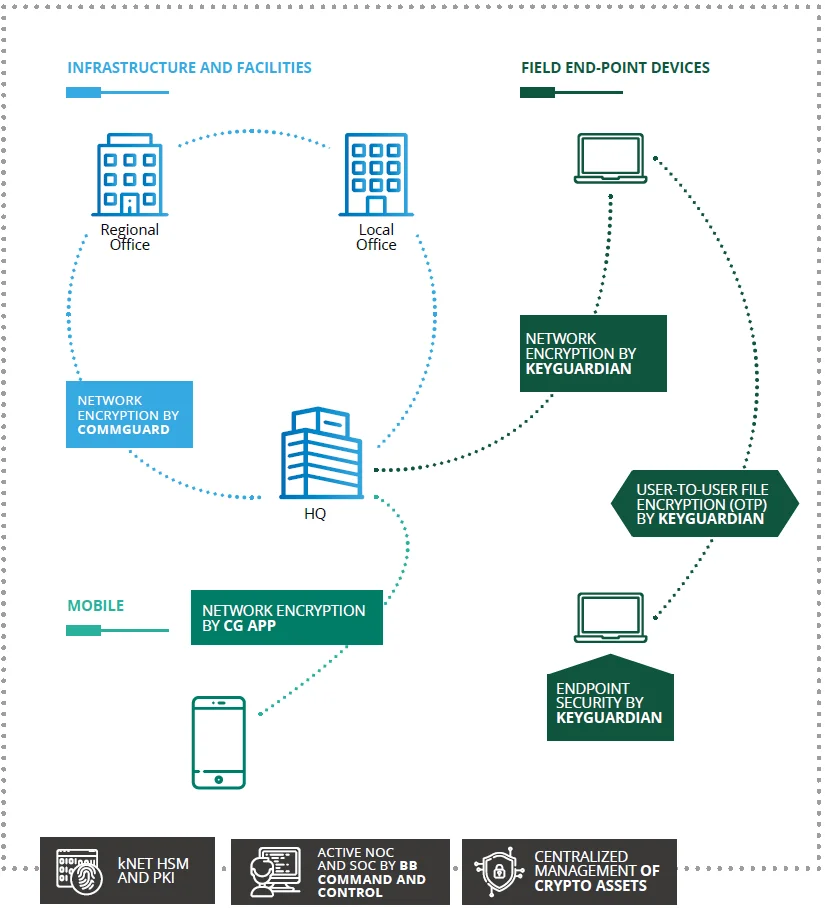
BruitBlanc infrastructure diagram.
2.2. The Anchor of Trust: kNET HSM
The Kryptus kNET HSM is the cryptographic heart of a sound PQC migration strategy. It serves as a dedicated, tamper-resistant hardware environment for the entire lifecycle of cryptographic keys: their generation, management, protection, and use. It functions as the root of trust for the entire security infrastructure, securing the new PQC-based Public Key Infrastructure (PKI) and protecting critical applications and databases where data is stored.
The kNET HSM is engineered to be PQC-native, with explicit support for the official NIST-standardized post-quantum algorithms:
– ML-DSA for quantum-resistant digital signatures.
– ML-KEM for quantum-resistant key establishment.
More important than the claim of support is the verifiable proof. The kNET HSM’s trustworthiness is established through a triad of globally recognized certifications, each addressing a critical aspect of security assurance.
– Common Criteria EAL4+: This certification, based on the ISO/IEC 15408 international standard, is evidence of a rigorous, methodical, and independently verified evaluation of the HSM’s security architecture and functions. Crucially, it is augmented with ALC_FLR.3, which guarantees a process for timely automatic distribution and user registration for flaw correction—a high-assurance feature for long-term security maintenance. For government and defense procurement, an EAL4+ rating is often a baseline requirement, signifying that the product has been formally tested and found to be robust against skilled, methodical attackers. It provides high assurance that the security claims of the product are sound and have been validated by an accredited third-party laboratory.
– NIST CAVP Validation for PQC: This is the critical proof of correct implementation. While any vendor can claim to use NIST’s algorithms, the Cryptographic Algorithm Validation Program (CAVP) provides official confirmation from NIST that the specific implementation of ML-DSA and ML-KEM inside the kNET HSM is mathematically correct and conforms precisely to the published standard. This is a non-negotiable guarantee of compliance and interoperability, eliminating the significant risk of deploying a flawed or non-standard algorithm that could contain hidden vulnerabilities.
– FIPS 140-2 Level 3: This U.S. government standard is another cornerstone of trust, specifically focused on the physical security of the cryptographic module. Level 3 certification indicates that the kNET HSM incorporates strong physical security mechanisms, including tamper-evidence and active tamper-response capabilities, designed to protect the sensitive cryptographic keys within from physical attacks. This level of physical hardening is essential for devices tasked with protecting national security information.
2.3. Securing Data-in-Transit: CommGuard Network Encryptor
The Kryptus CommGuard (CG) is the shield for data in motion. It is a high-performance network encryptor designed to create secure Virtual Private Networks (VPNs) and protect all IP traffic flowing between headquarters, distributed sites, and remote field operations.
To counter the quantum threat to data-in-transit, the CommGuard integrates support for ML-KEM, the NIST standard for quantum-resistant key exchange. The implementation of this algorithm follows the same rigor required by the NIST CAVP certification obtained by the kNET HSM, ensuring a correct and compliant deployment. This ensures that the secure communication channels established by CommGuard are protected against both current and future eavesdropping attacks, including HNDL campaigns.
2.4. Securing the Edge: KeyGuardian Portable Cryptocomputer
The Kryptus KeyGuardian extends quantum-safe security to the most vulnerable and distributed part of the network: the endpoint. It is a portable, USB-based hardware security device designed for personnel in the field, securing laptops, enabling secure remote access to networks protected by CommGuard, and encrypting sensitive documents and communications at their point of creation.
KeyGuardian provides a unique dual-pronged approach to ultimate security. It is engineered with the ML-KEM algorithm embedded, the NIST standard for quantum-resistant key exchange, to future-proof endpoint security. Simultaneously, it offers One-Time Pad (OTP) encryption, a method that is information-theoretically secure. Unlike computational security, which relies on the difficulty of a math problem, OTP is proven to be unbreakable by any computer, regardless of its power—classical, quantum, or otherwise. This provides an unparalleled, failsafe level of security for today’s most ultra-sensitive, classified communications, complementing the forward-looking protection of PQC.
| Component | Primary Role | PQC Algorithms Supported |
| kNET HSM | Cryptographic Root of Trust; PQC Key Generation & Protection; PKI Management; Data-at-Rest Encryption | ML-DSA, ML-KEM |
| CommGuard | Network Traffic Encryption (Data-in-Transit); Secure Site-to-Site VPNs | ML-KEM |
| KeyGuardian | Endpoint Security; Secure Remote Access; Document Encryption & Signing | ML-KEM (and OTP) |
The following table translates these technical certifications into the language of executive assurance, clarifying what each credential means for organizational risk management and due diligence.
| Certification | Issuing Body/Standard | What It Means for Your Organization |
| Common Criteria EAL4+ | ISO/IEC 15408 | Provides high, independently verified assurance that the product’s security architecture is sound and has been rigorously tested. The inclusion of ALC_FLR.3 guarantees a process for timely, automatic security updates for flaw correction. A key requirement for deploying technology in high-security government and defense environments. |
| NIST CAVP (for PQC) | U.S. National Institute of Standards and Technology | Guarantees that the implementation of the new quantum-resistant algorithms is mathematically correct and conforms to the official U.S. government standard. This is non-negotiable proof of compliance and interoperability. |
| FIPS 140-2 Level 3 | U.S. Federal Information Processing Standard | Confirms the hardware has strong physical security, including tamper-evidence and tamper-response mechanisms, to protect the cryptographic keys within. Essential for protecting national security information. |
Section 3: A Practical 4-Step Migration Roadmap with Kryptus
3.1 Confronting the Migration Challenge
It is essential to acknowledge that the migration to Post-Quantum Cryptography is one of the most significant and complex cybersecurity undertakings in decades. It is not a simple “patch and pray” exercise but a systemic overhaul of foundational security infrastructure. Organizations must prepare for several key hurdles:
– Performance and Infrastructure Impact: The new PQC algorithms often have significantly larger key sizes and digital signatures compared to their classical predecessors. This can increase demands on network bandwidth, data storage, and computational processing power, potentially necessitating upgrades to network infrastructure, servers, and constrained devices.
– Systemic and Application-Level Changes: Migration requires updating core communication protocols like TLS and IPsec, as well as modifying countless software libraries and applications across the entire technology stack to support the new cryptographic primitives.
– Cryptographic Expertise Shortage: There is a pronounced global shortage of engineers and cryptographers with practical, hands-on experience in implementing PQC algorithms and protocols correctly. This skills gap presents a significant risk of implementation errors and project delays.
– Fragmented and Undocumented Systems: Large government and defense organizations often operate vast, heterogeneous IT environments with a chaotic and poorly documented “cryptographic inventory.” This fragmentation makes the initial task of simply identifying all instances of vulnerable cryptography a monumental challenge.
The Kryptus BruitBlanc ecosystem is designed not only to provide the necessary PQC technology but also to create a structured framework that simplifies and de-risks this complex migration process.
Step 1: Discover and Prioritize – Building the Cryptographic Inventory
The foundational first step of any PQC migration, as mandated by guidance from NIST and CISA, is to create a comprehensive inventory of all systems, applications, and data flows that use public-key cryptography. An organization cannot protect what it does not know it has. This discovery process is critical for understanding the full scope of the migration effort, identifying mission-critical systems, and prioritizing the transition based on data sensitivity and risk.
While this can be a daunting task, the process of planning a strategic deployment of the BruitBlanc ecosystem inherently forces a structured approach to this inventory. By designating the kNET HSM as the future central authority for PQC-based digital certificates and key management, organizations are compelled to identify the critical systems, applications, and network endpoints that will need to trust and interact with this new root of trust. This planning phase effectively kick-starts the discovery process in a managed, top-down manner, focusing first on the most critical assets that require the highest level of security.
Step 2: Fortify the Core – Securing the Root of Trust with kNET HSM
The most logical and secure place to begin the active migration is at the very core of the cryptographic infrastructure: the generation, protection, and management of keys. Deploying the certified, PQC-ready kNET HSM as the new cryptographic root of trust is the foundational move that anchors the entire migration strategy.
This step directly confronts the critical challenge of fragmented key management. In many organizations, cryptographic keys are generated and stored in a decentralized and inconsistent manner across various applications and systems. By establishing the kNET HSM as the central, authoritative source for all new PQC keys and certificates, an organization creates a “single source of truth” for its most sensitive assets. This imposes order on cryptographic chaos and establishes a secure beachhead from which the rest of the migration can be safely and methodically expanded. All new PQC-enabled systems will draw their cryptographic trust from this fortified, certified, and centrally managed core.
Step 3: Secure the Arteries – Protecting Data-in-Transit with CommGuard
Once the cryptographic core is secured, the next logical priority is to protect the data flowing between secure locations. This involves a phased rollout of CommGuard network encryptors on critical communication links, such as those connecting headquarters to regional offices, data centers, and key operational sites.
This phase is the ideal point to implement a PQ/Traditional hybrid approach to ensure a smooth transition. During the migration period, many systems will not yet be PQC-enabled. A hybrid key exchange scheme allows the CommGuard to establish a secure channel using both a classical algorithm (like Elliptical Curves) and a PQC algorithm (ML-KEM) in parallel. The final session key is derived from both computations, ensuring that the connection is at least as secure as today’s proven cryptography while simultaneously adding resistance to quantum attacks. This approach mitigates risk, prevents service disruptions, and ensures backward compatibility and interoperability with legacy systems that have not yet been upgraded.

A 6-step diagram of the CommGuard Hybrid Key Mechanism.
Step 4: Extend to the Edge – Protecting Endpoints with KeyGuardian
The final phase of the roadmap is to extend quantum-resistant protection to the most distributed and often most vulnerable assets: endpoints used by personnel in the field. This involves deploying KeyGuardian portable security devices to remote workers, diplomats, field agents, and other mobile users.
This step completes the end-to-end security chain. With KeyGuardian, data is protected from its point of creation on an endpoint device, secured by CommGuard as it traverses the network, and finally protected at rest in databases and applications that derive their security from the kNET HSM. This achieves true, comprehensive, end-to-end quantum-resistant security across the entire operational landscape, from the central data center to the furthest operational edge.
| Migration Challenge | Typical Impact | The BruitBlanc Solution |
| Lack of PQC Expertise | Risk of incorrect implementation, project delays, introduction of new vulnerabilities. | kNET HSM provides a turnkey, certified hardware solution with NIST CAVP-validated algorithms, abstracting away the deep cryptographic complexity and ensuring a correct-by-design implementation. |
| Hardware/HSM Upgrades | High cost and disruption of replacing legacy HSMs not designed for PQC performance characteristics. | kNET HSM is a modern, PQC-native HSM designed for this transition, offering a clear upgrade path with features like virtual HSMs for cost-effective consolidation of cryptographic services. |
| Fragmented Key Management | No central visibility or control, making a systematic migration chaotic and prone to gaps. | Deploying the kNET HSM as the central Root of Trust (Step 2) establishes a unified cryptographic core, solving fragmentation at its source and providing a single point of management and audit. |
| Interoperability During Transition | Need to support both PQC-enabled and legacy systems simultaneously without breaking connectivity. | CommGuard’s support for hybrid key exchange modes allows for a phased rollout, ensuring new PQC-enabled networks can still communicate securely with legacy systems. |
| Securing Field Operations | Extending high-assurance protection to vulnerable mobile and remote endpoints is notoriously complex. | KeyGuardian provides a portable, hardware-based solution for endpoints, offering both embedded ML-KEM for future-proofing and unbreakable OTP for current ultra-sensitive data, managed within the same ecosystem. |
Conclusion: Achieving Crypto-Agility and Sovereign Security
The migration to Post-Quantum Cryptography is a necessary response to a specific, foreseeable technological threat. However, the ultimate strategic goal for any forward-looking organization should not be a one-time fix, but the establishment of a permanent state of “crypto-agility”. Crypto-agility is the organizational and technical capability to rapidly adapt to future cryptographic threats and evolving standards without requiring another disruptive, multi-year, and costly overhaul of the entire infrastructure. The current PQC migration should be viewed as the first major test of an organization’s crypto-agility—and an opportunity to build the policies, inventory systems, and modular architecture needed to master future transitions.
Kryptus BruitBlanc ecosystem provides the practical, certified, and integrated toolkit to not only execute the immediate PQC migration but also to build this lasting foundation of crypto-agility. Its modular components—the certified kNET HSM core, the flexible CommGuard network layer, and the adaptable KeyGuardian endpoint—are designed to be managed and updated as part of a cohesive system, enabling future cryptographic transitions to be executed with far greater speed and lower risk.
Finally, for public and defense organizations, the choice of a cryptographic partner carries profound implications for national sovereignty. In an era of increasing geopolitical uncertainty and supply chain risks, relying on cryptographic solutions from foreign powers can introduce unacceptable vulnerabilities and dependencies. The BruitBlanc is explicitly designed as a sovereign solution, “free from surveillance laws,” offering a clear path to a quantum-safe future that simultaneously strengthens a nation’s technological independence. It ensures that a country’s most critical secrets, the bedrock of its security and sovereignty, remain unequivocally under its own control, today and in the quantum era to come.


